OKTA
Security Access Reviews
Helping security teams detect and remediate risky access faster with AI-driven insights.
Design challenge
Access Certifications satisfy audit and compliance needs well, but follow a reactive, scheduled cadence - typically quarterly - rather than responding dynamically to identity-based security incidents. Security teams have threat detection tools, but lack a direct way to act on identity threats in real time, leaving access reviews disconnected from real-time risk detection.
How might we bridge the gap between threat detection and access certifications to enable timely, risk-aware access decisions and support a more proactive security posture?
View case study
Skills applied
User research
User interface design
Usability testing
Artificial Intelligence
Prototyping
Product strategy
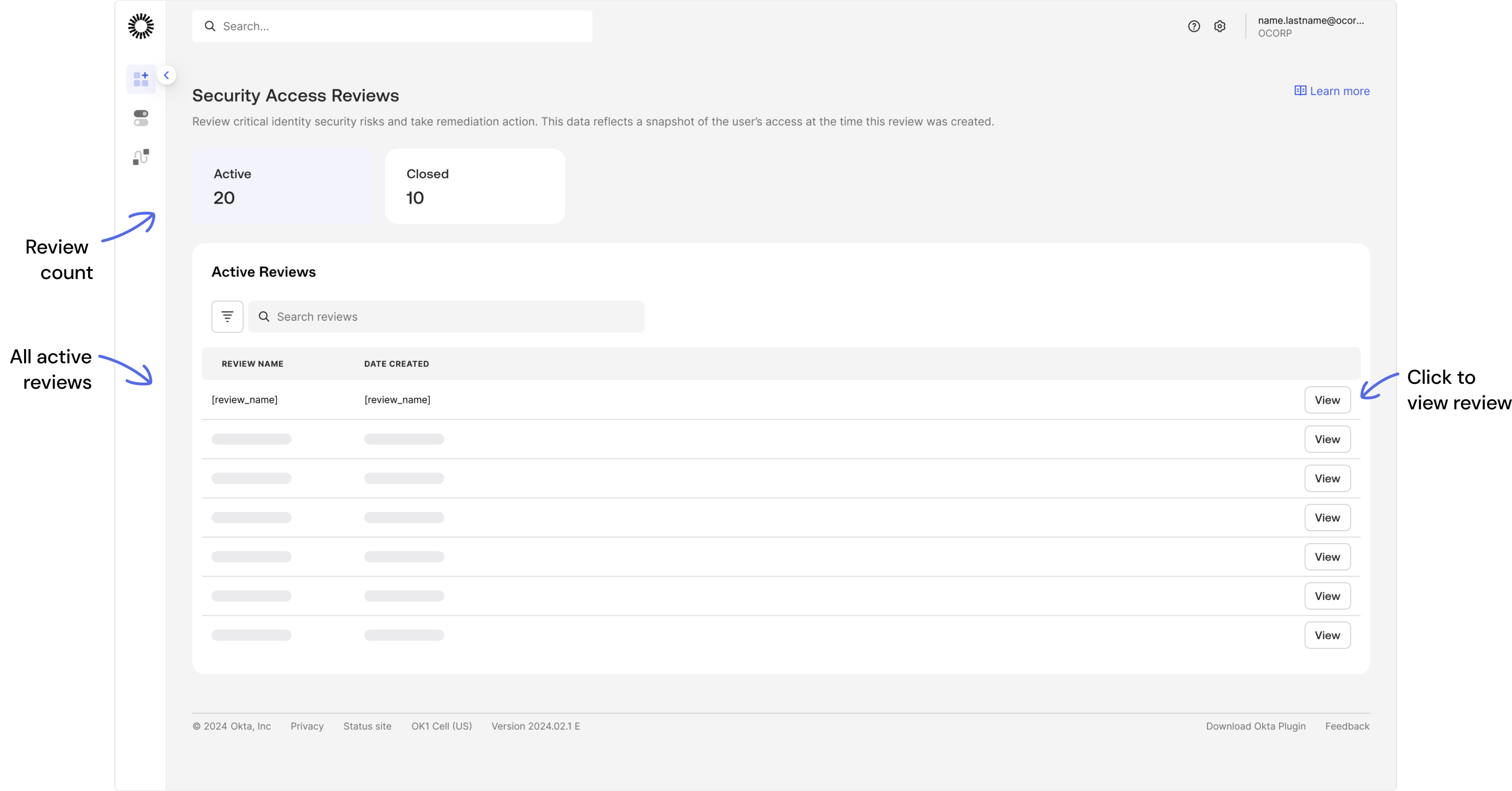
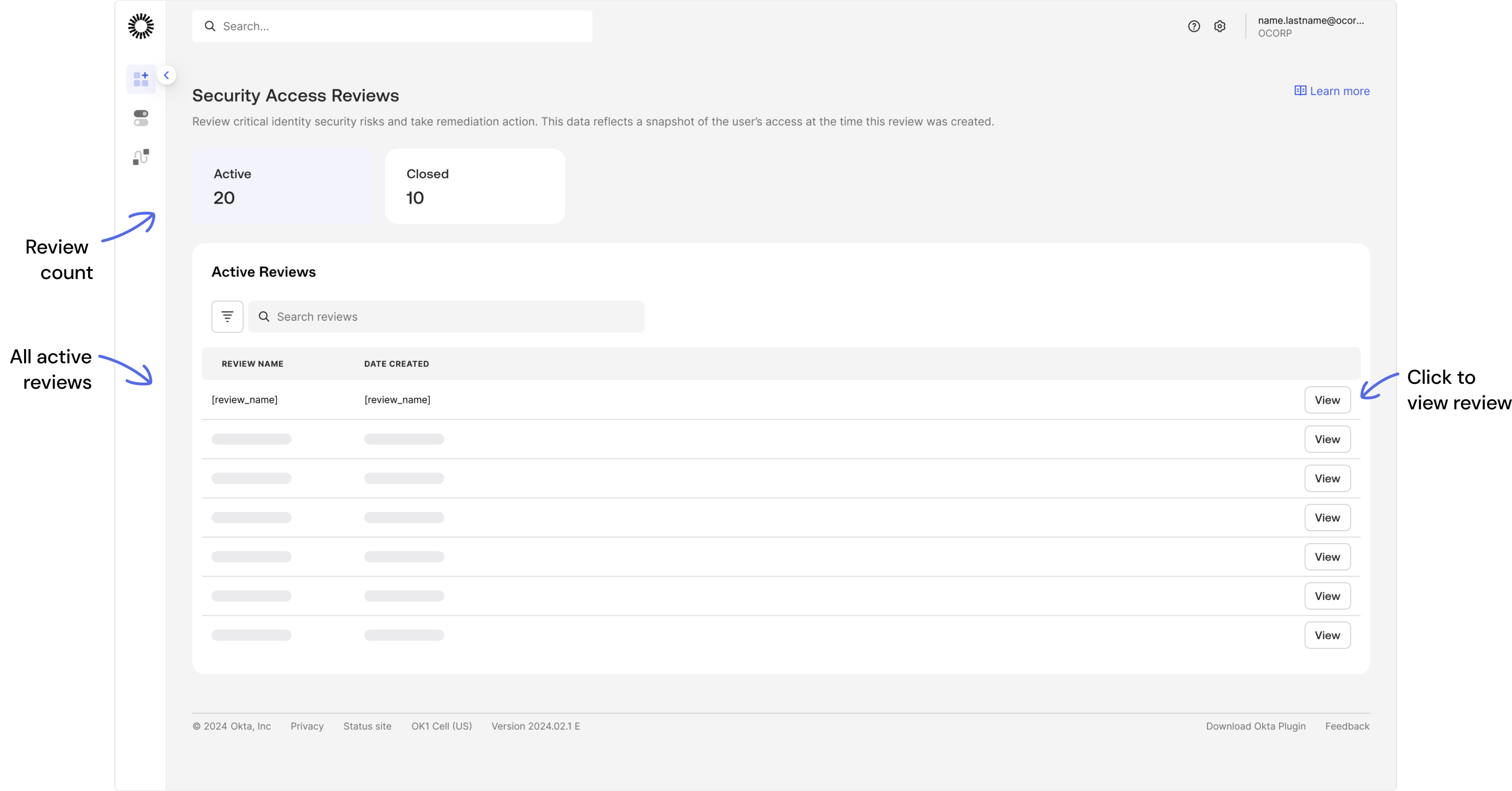
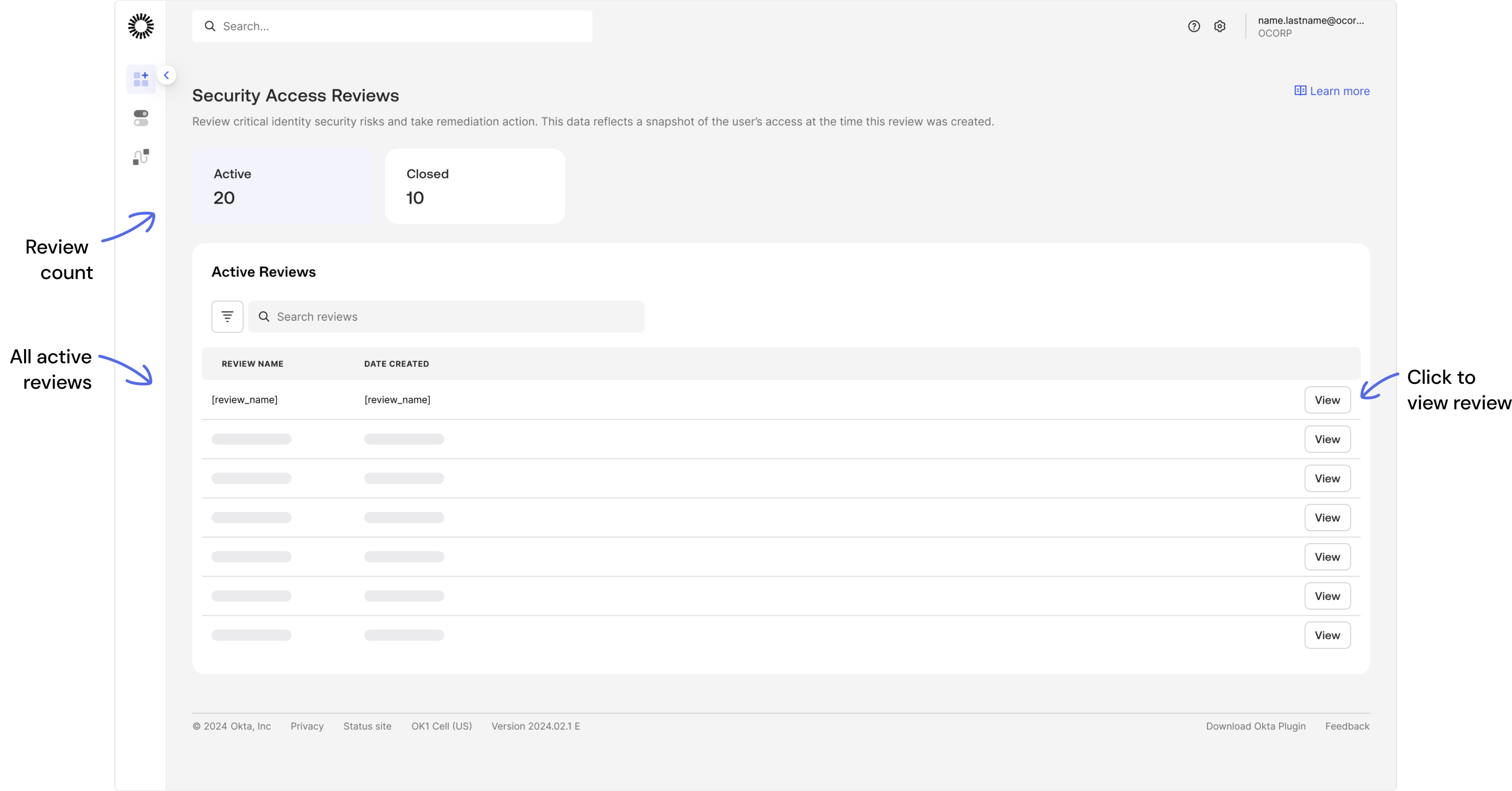
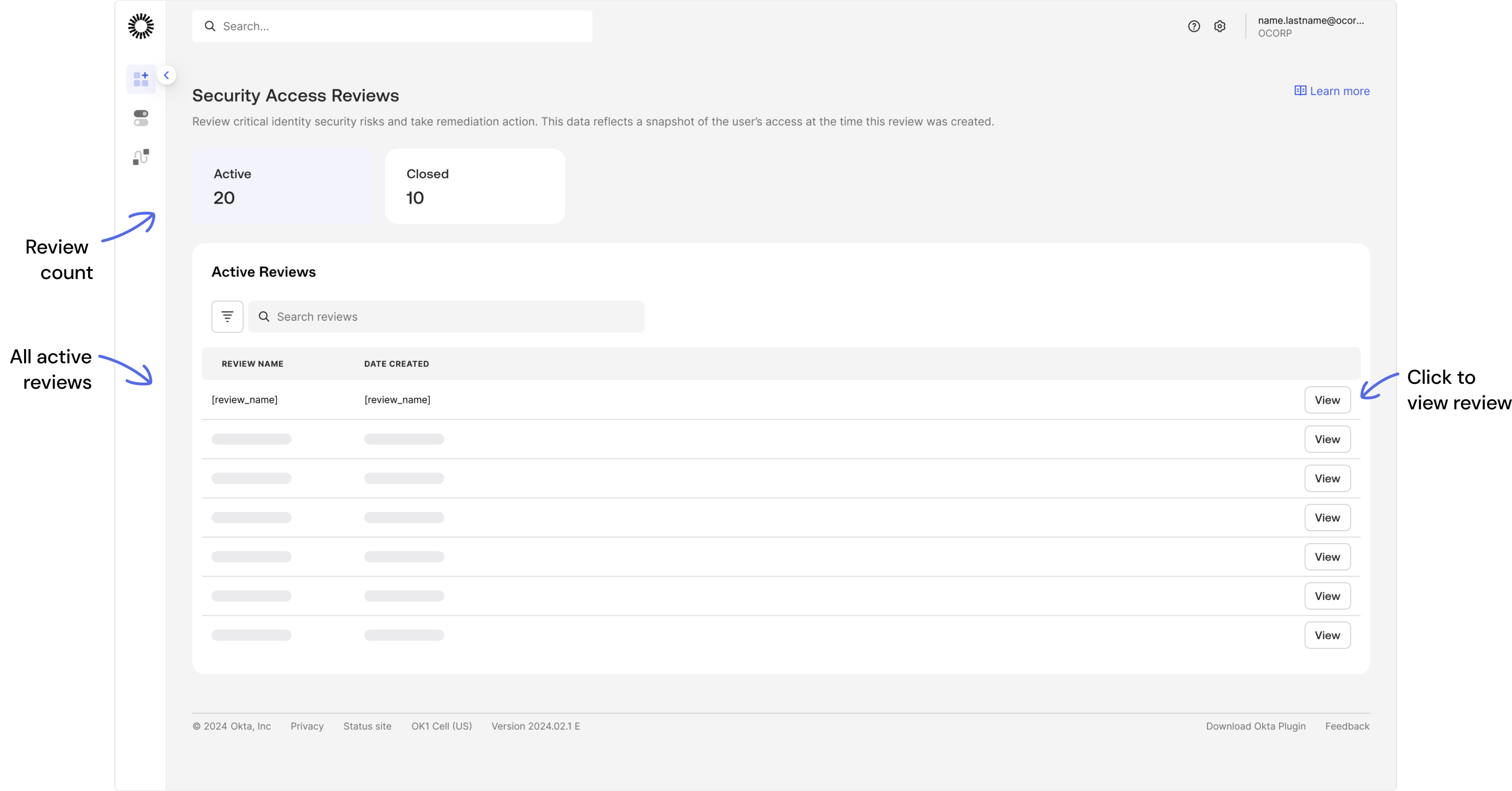
Home page
List of all active and closed access reviews
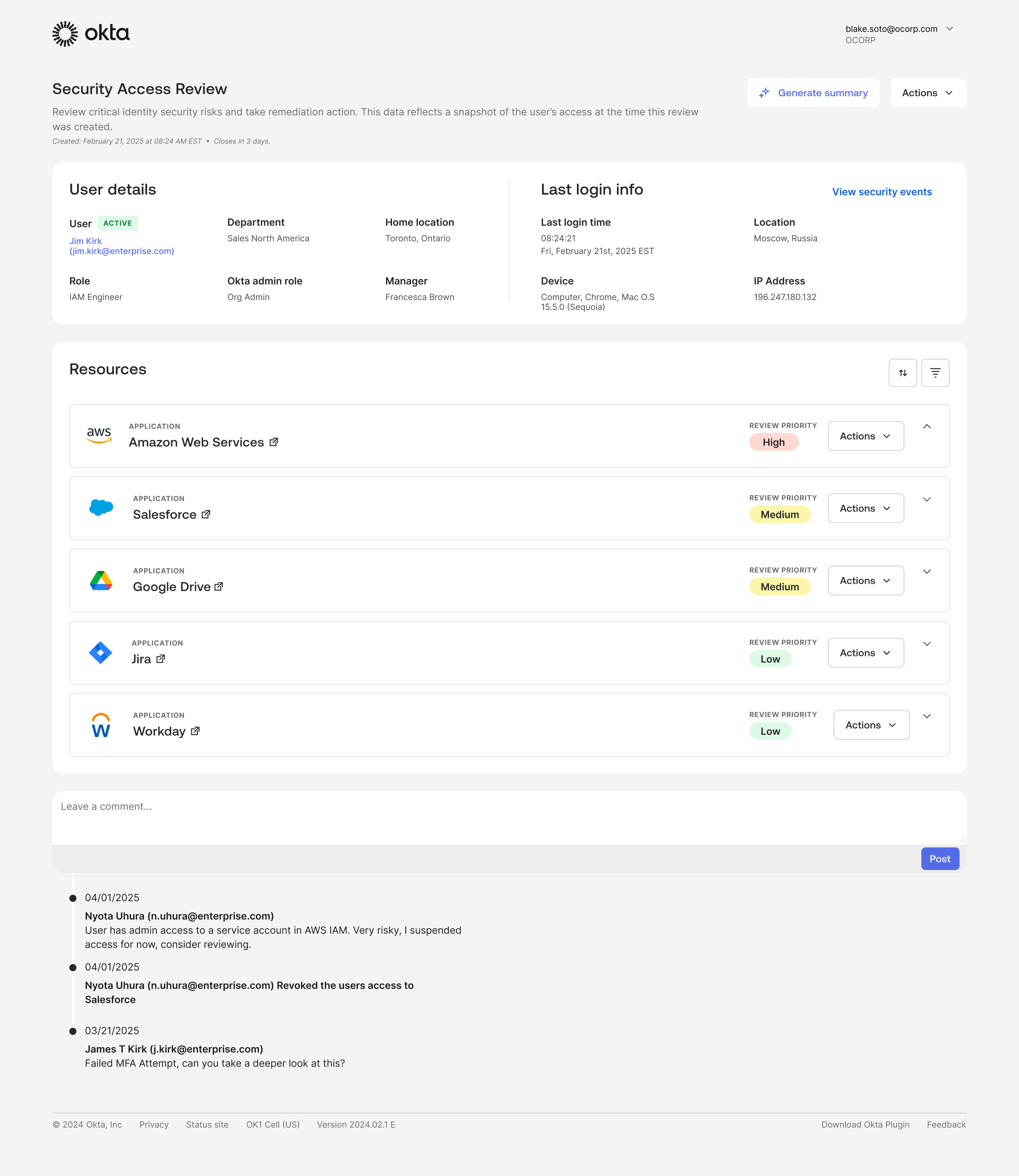
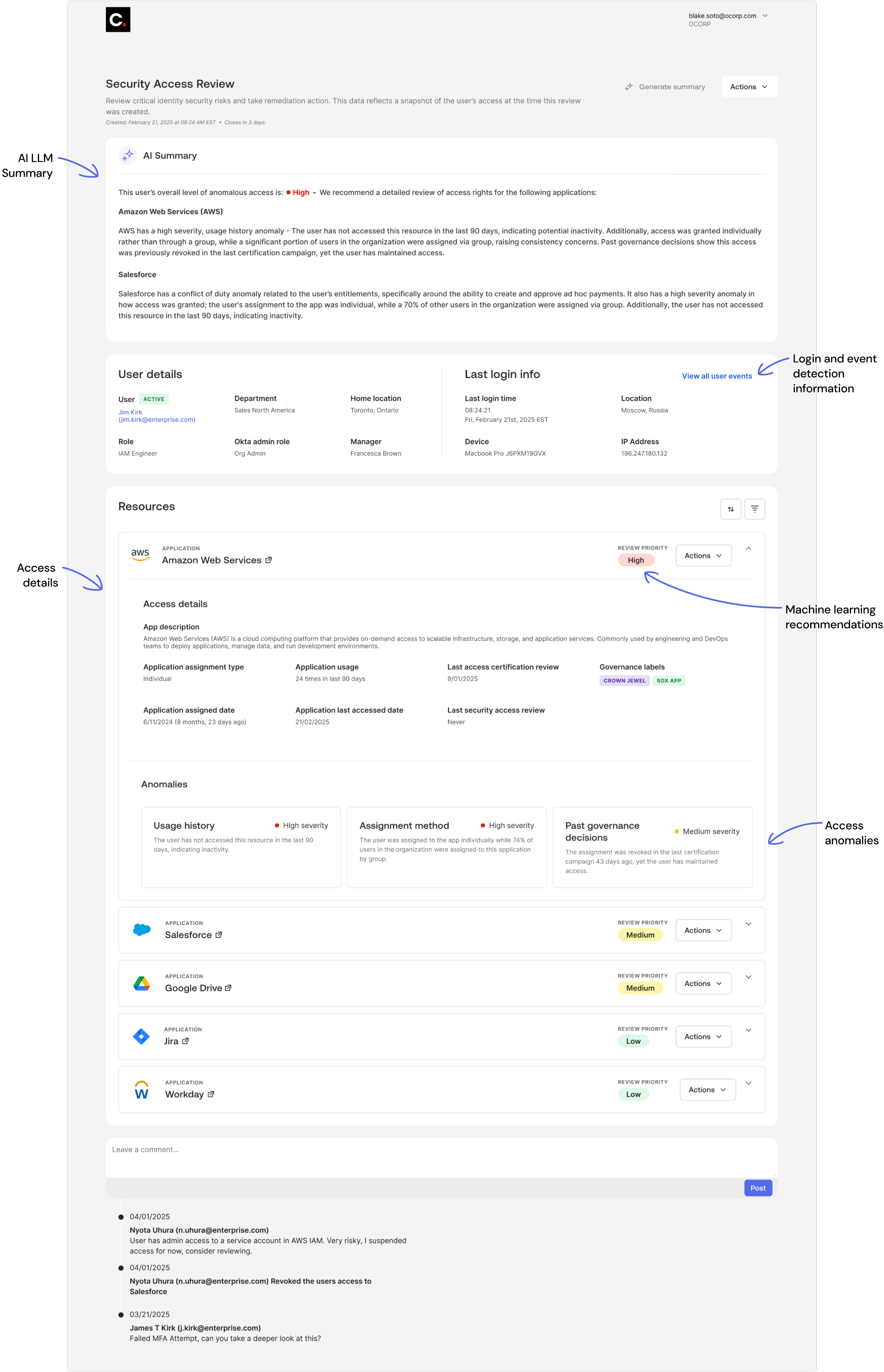
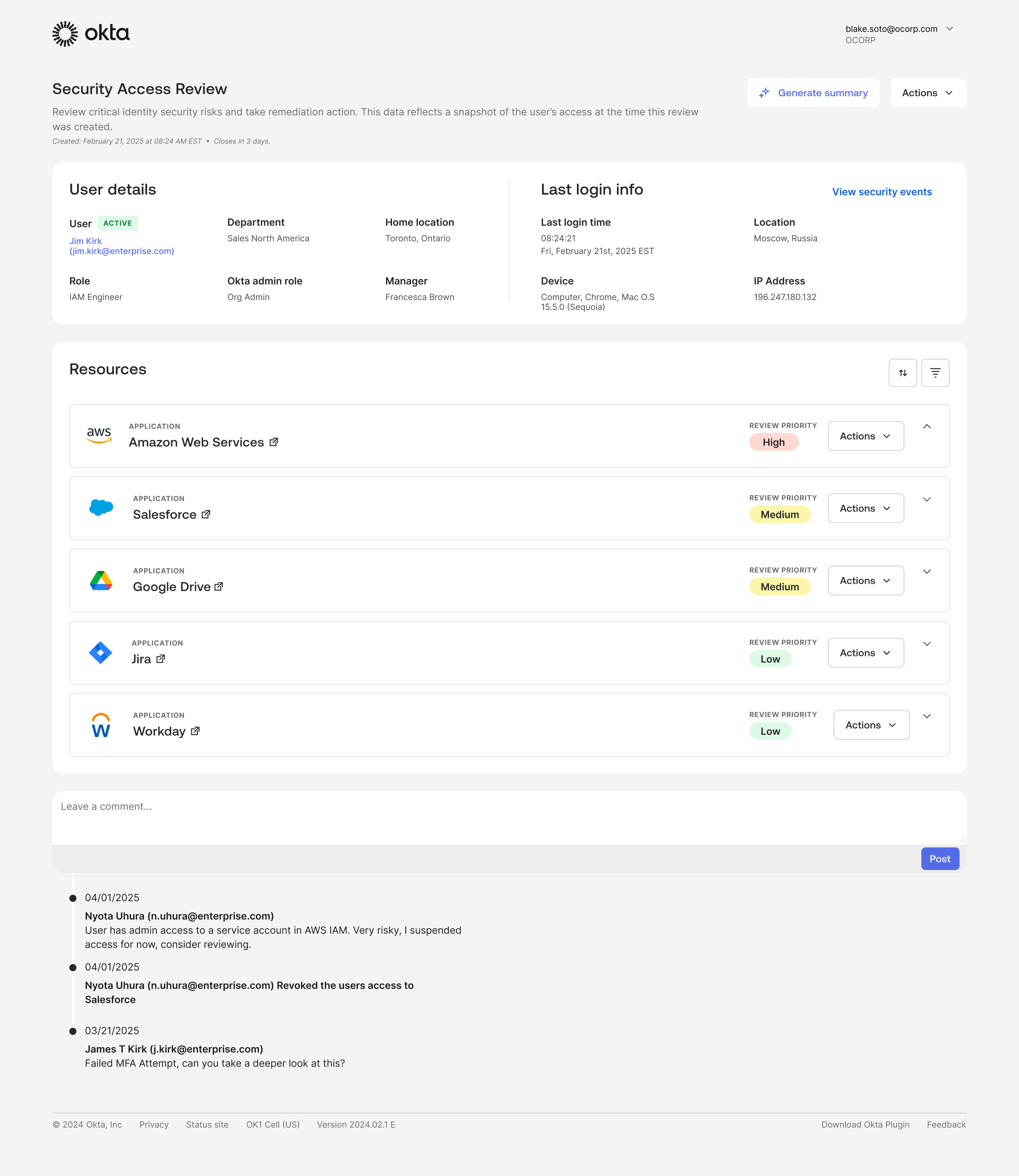
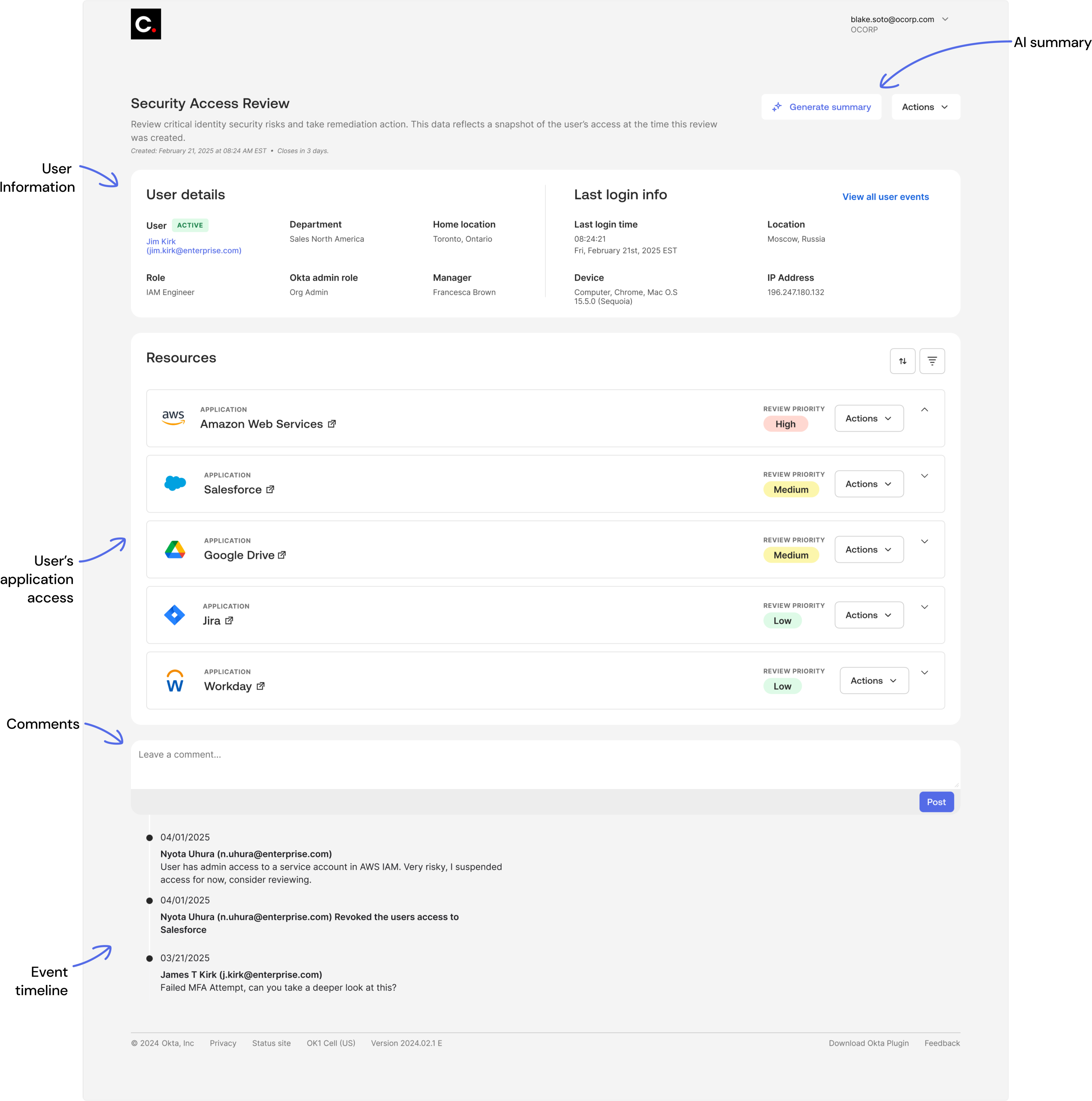
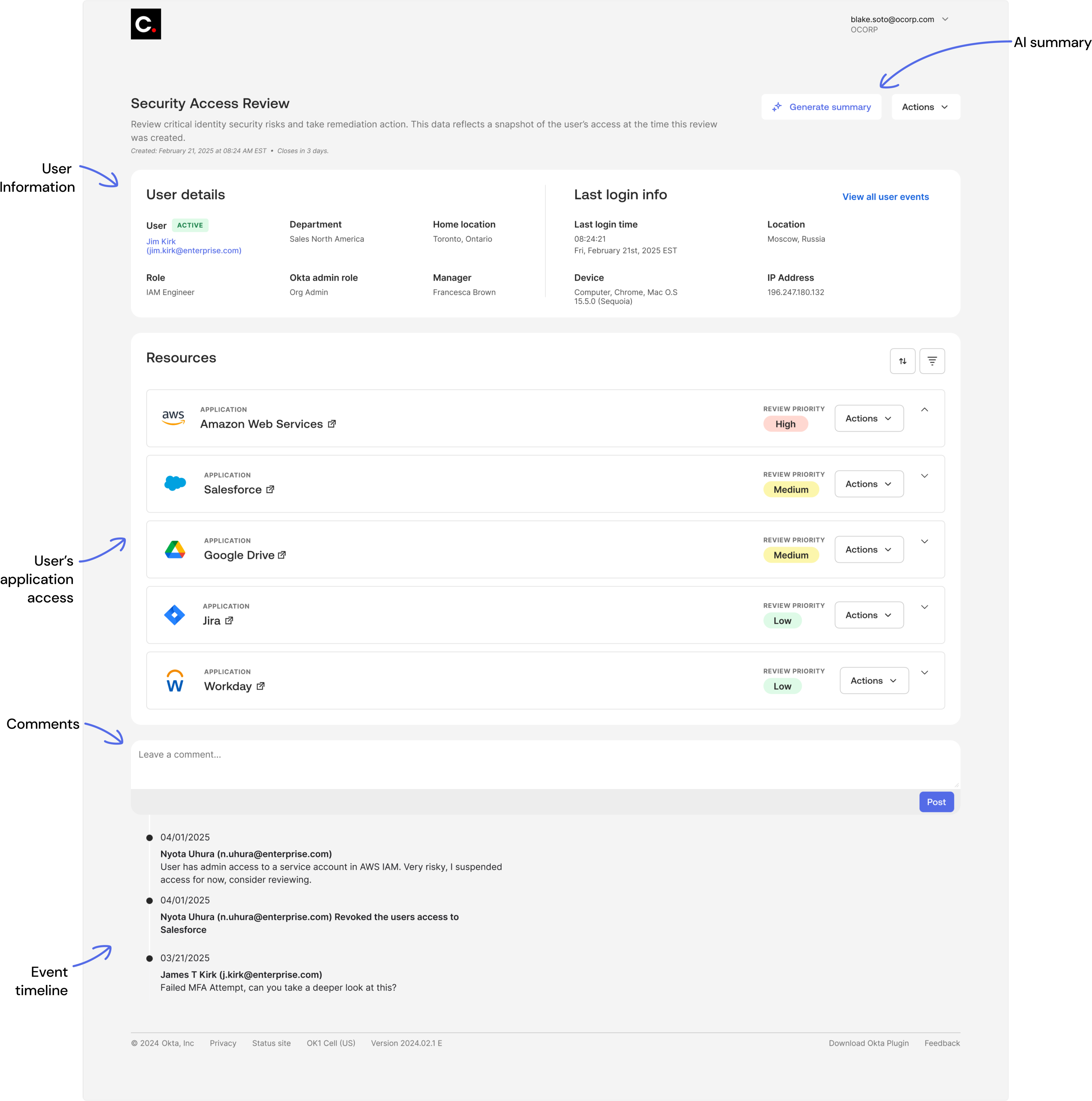
Active review
Reviewing user access and permissions for a specific employee
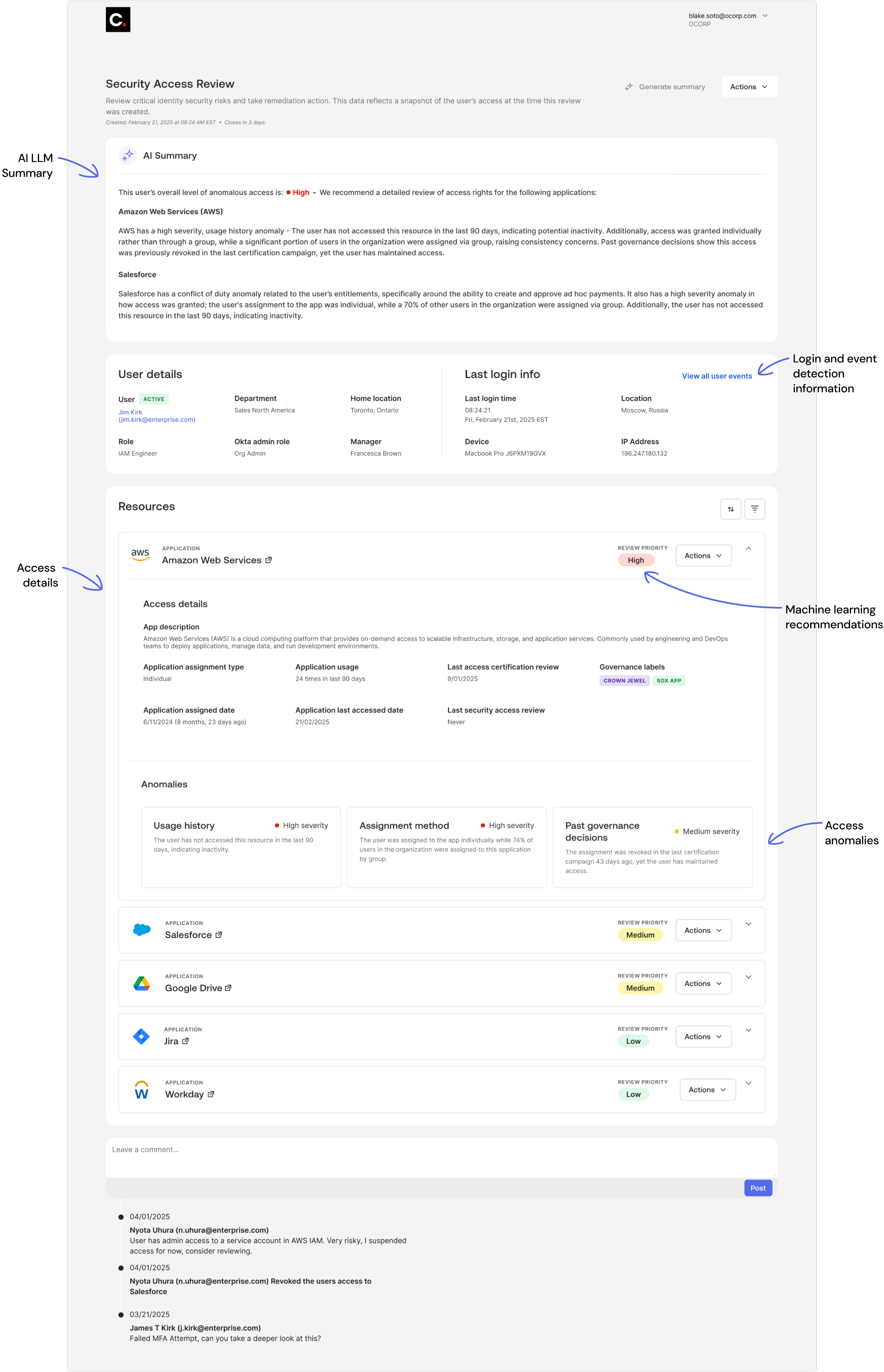
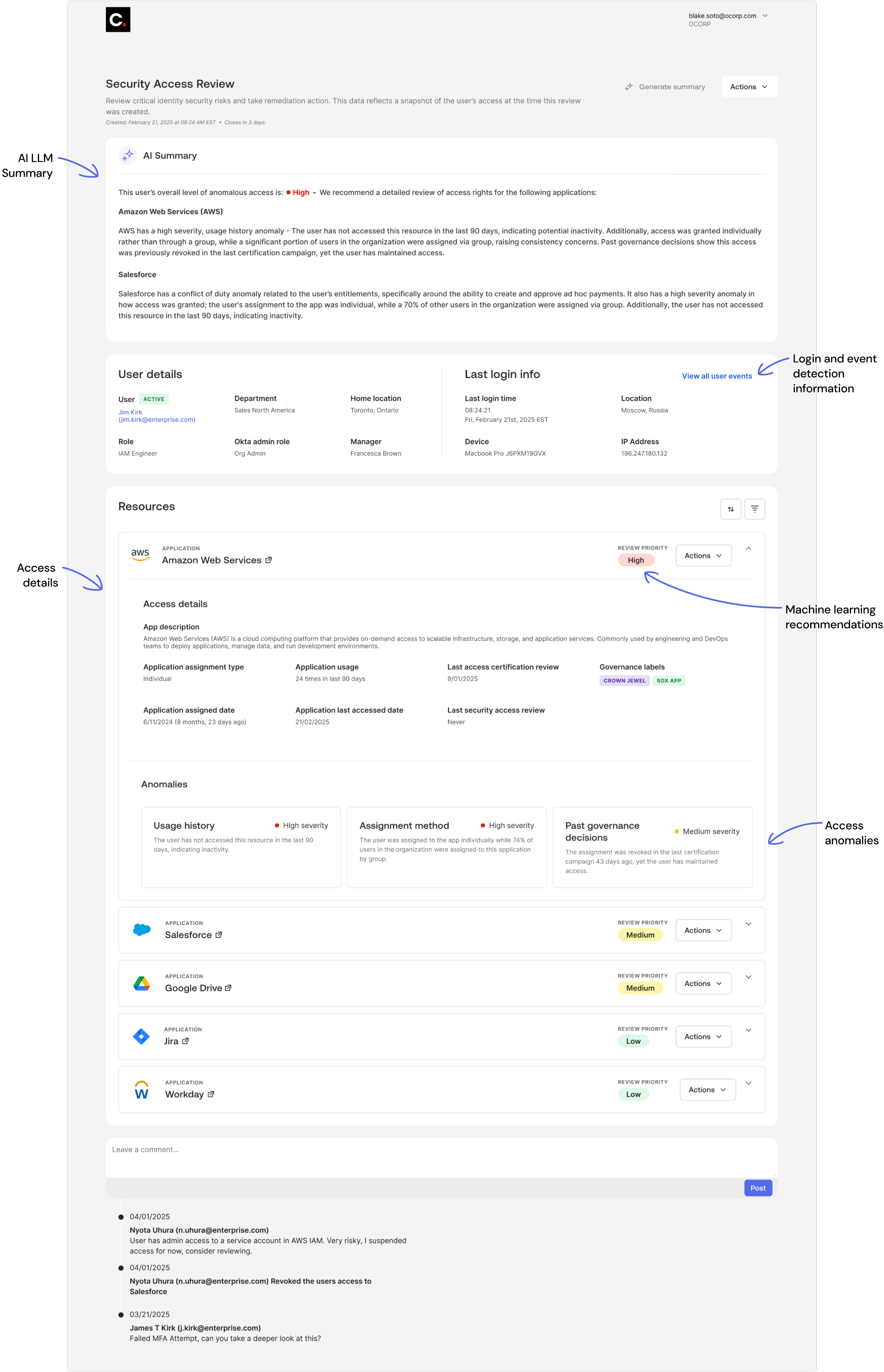
Active review
AI LLM summary & application details
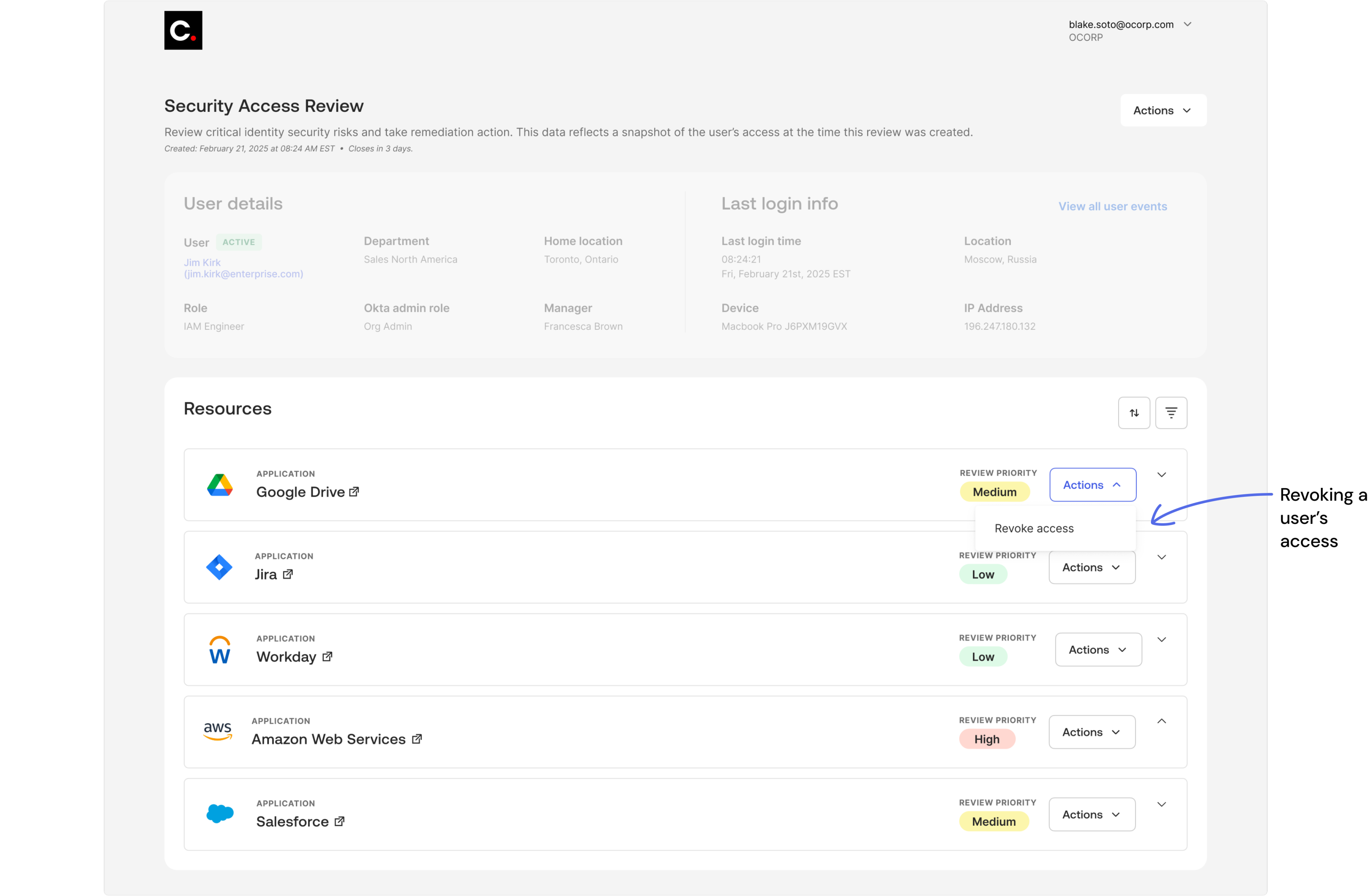
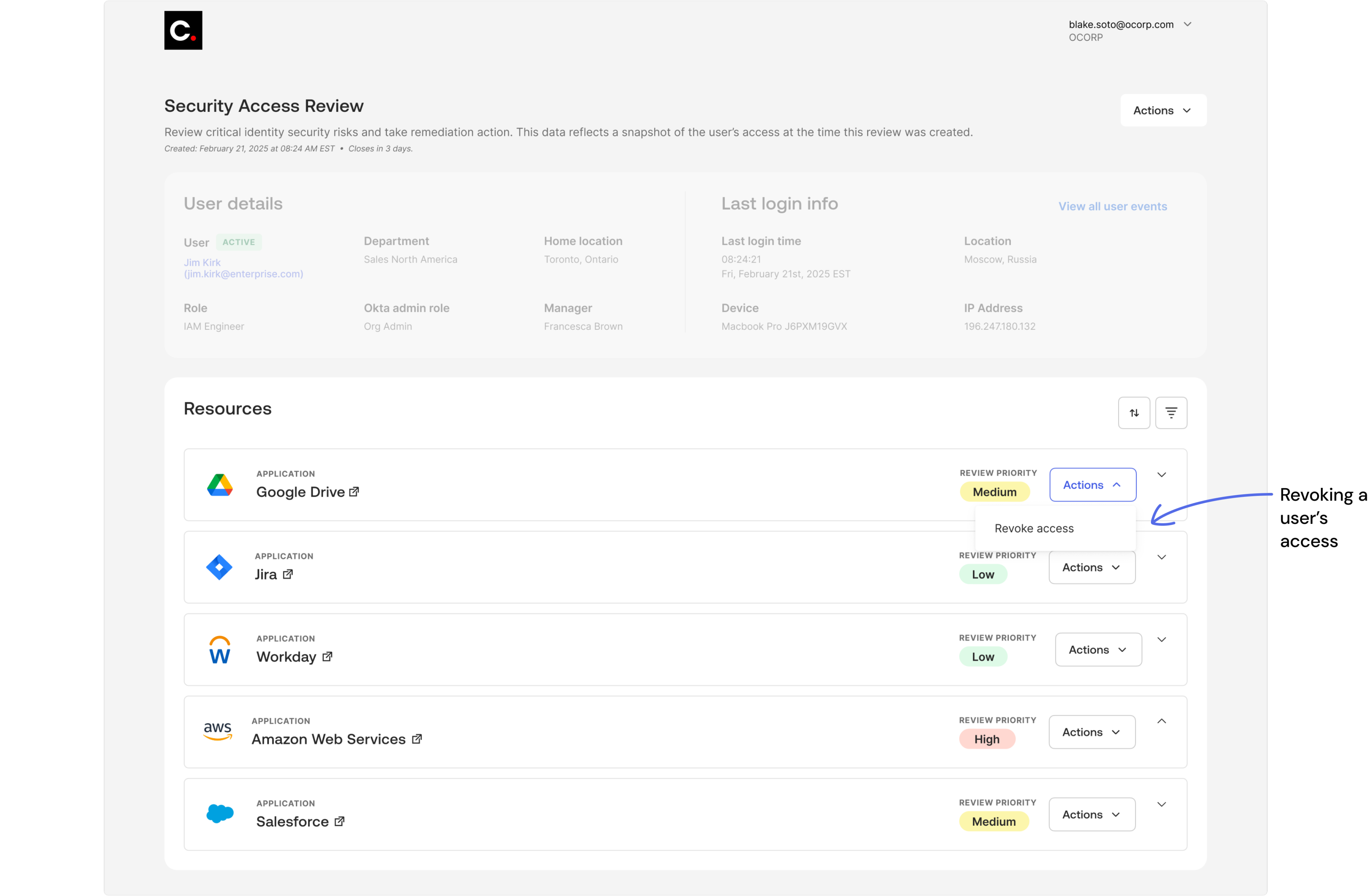
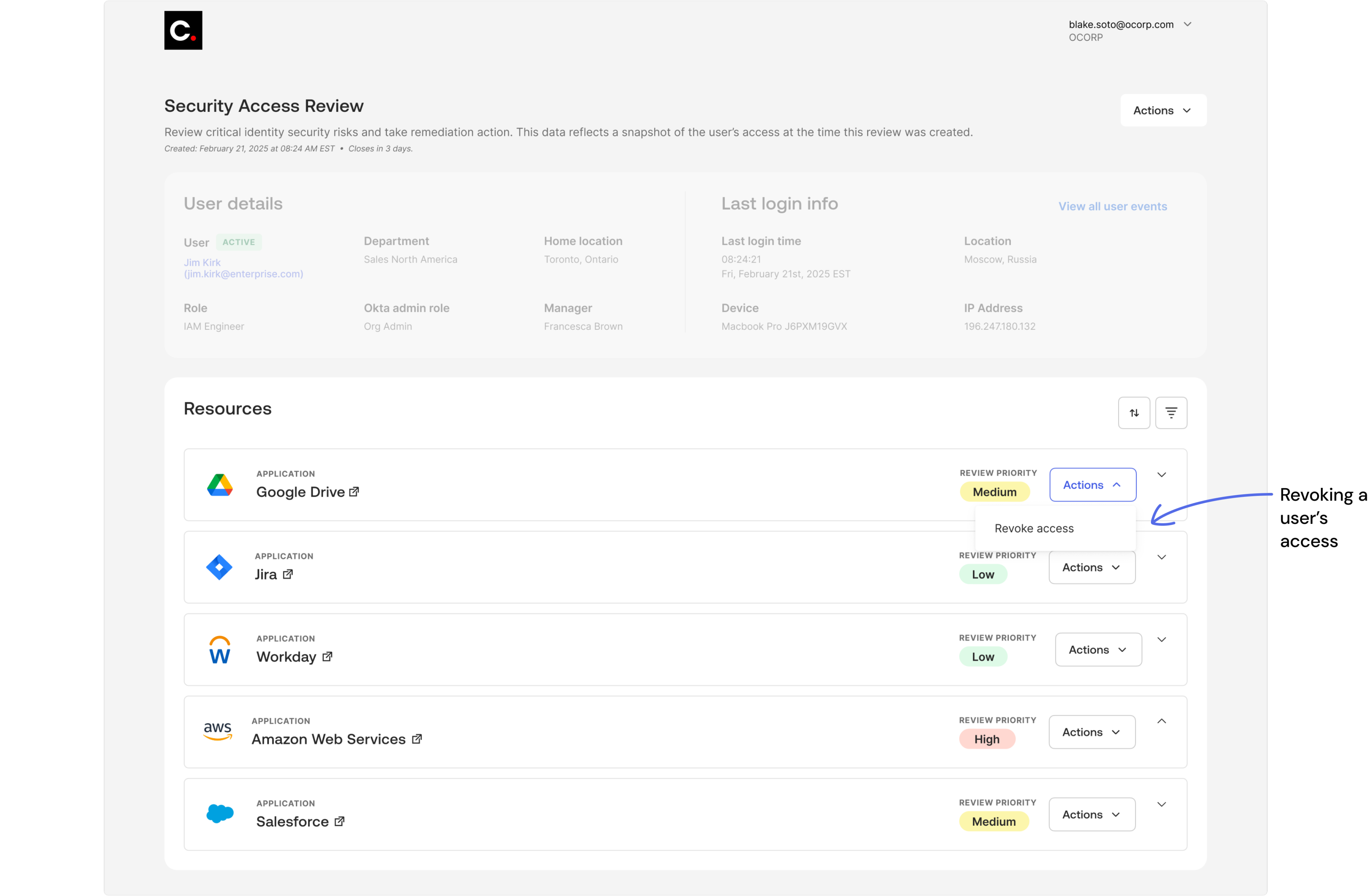
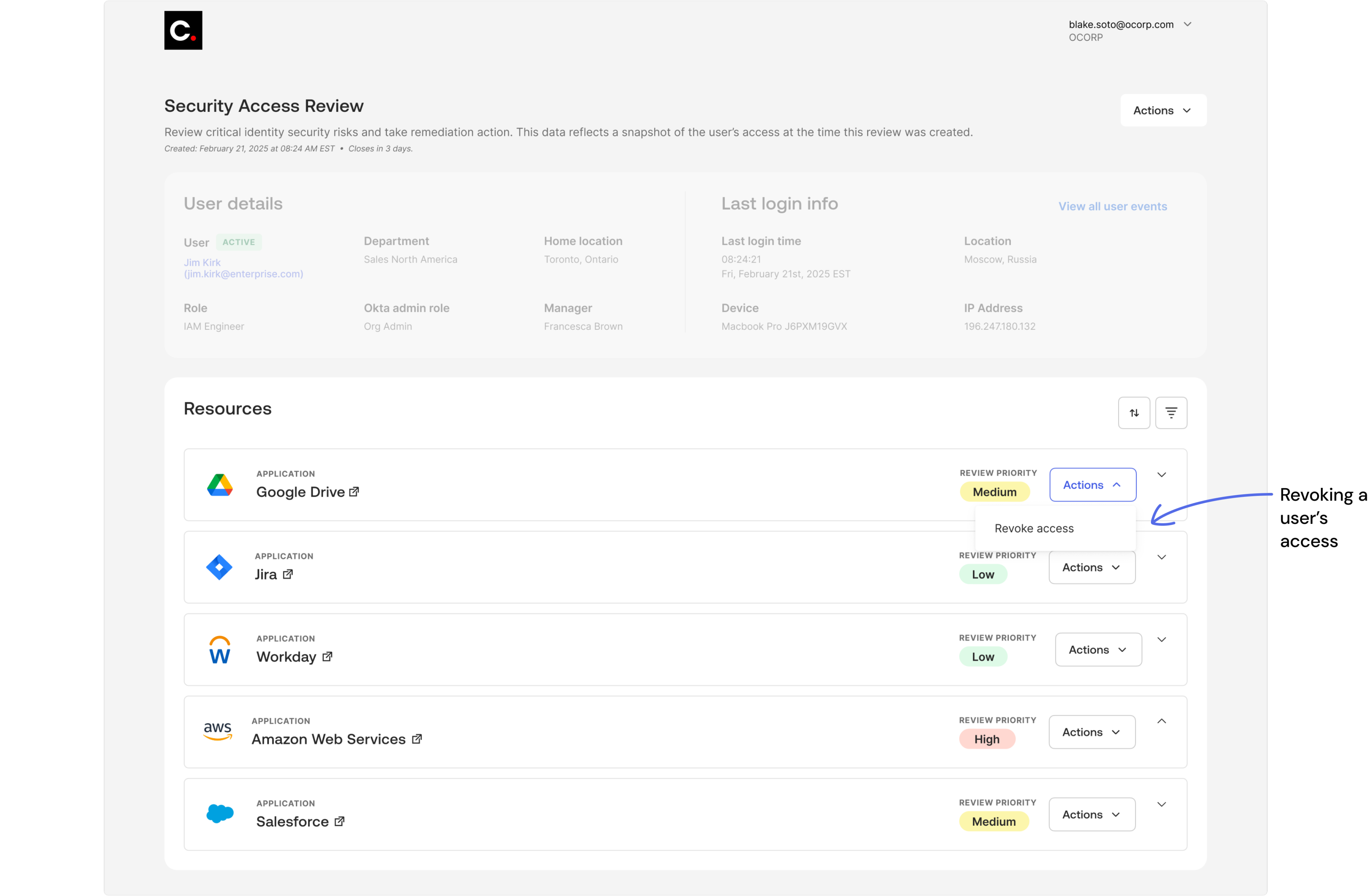
Remediation actions
Revoking a user’s access to an application
View UX Case Study
OKTA
Security Access Reviews
Helping security teams detect and remediate risky access faster with AI-driven insights.
Design challenge
Access Certifications satisfy audit and compliance needs well, but follow a reactive, scheduled cadence - typically quarterly - rather than responding dynamically to identity-based security incidents. Security teams have threat detection tools, but lack a direct way to act on identity threats in real time, leaving access reviews disconnected from real-time risk detection.
How might we bridge the gap between threat detection and access certifications to enable timely, risk-aware access decisions and support a more proactive security posture?
View case study
Skills applied
User research
User interface design
Usability testing
Artificial Intelligence
Prototyping
Product strategy
Home page
List of all active and closed access reviews
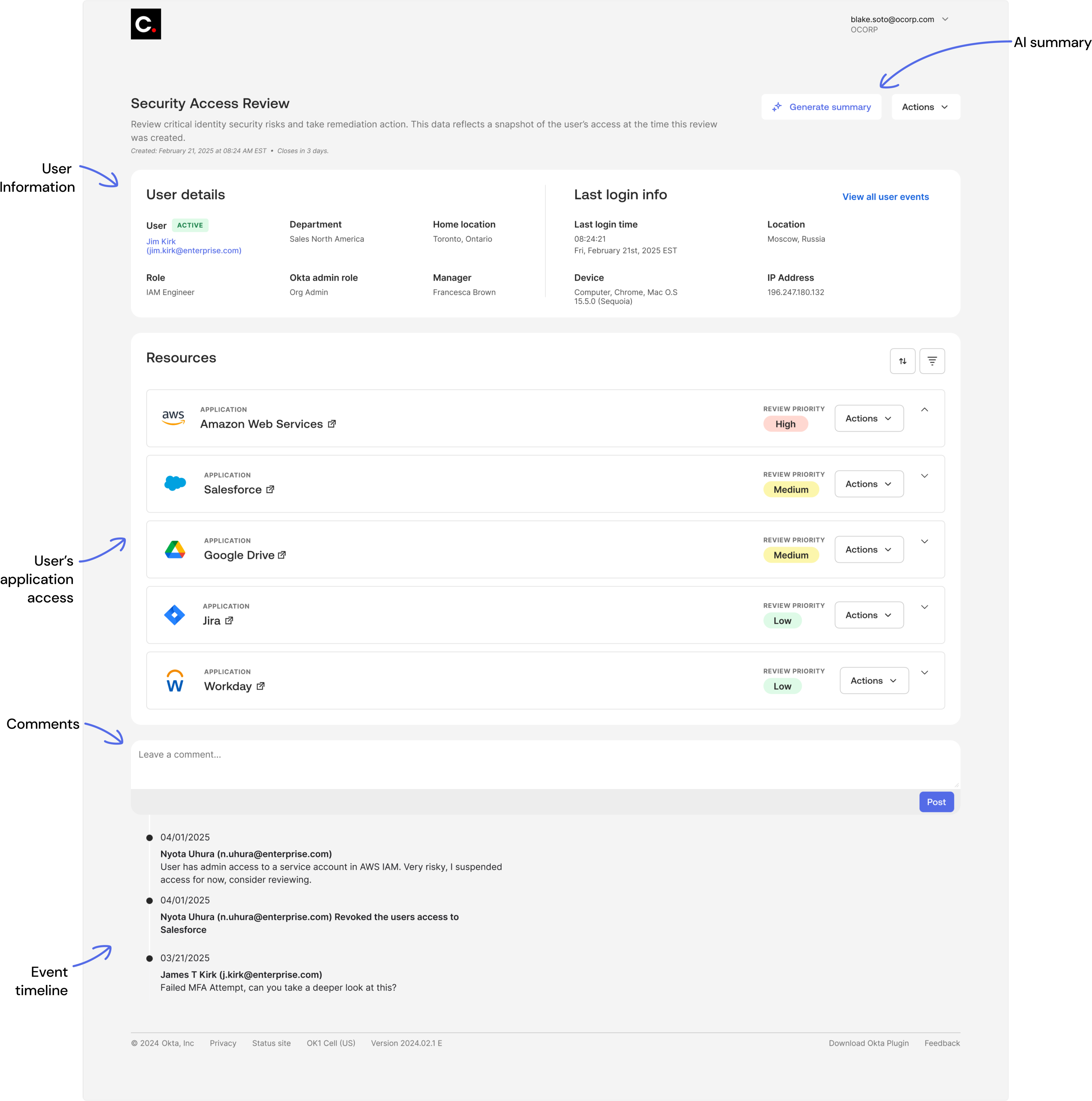
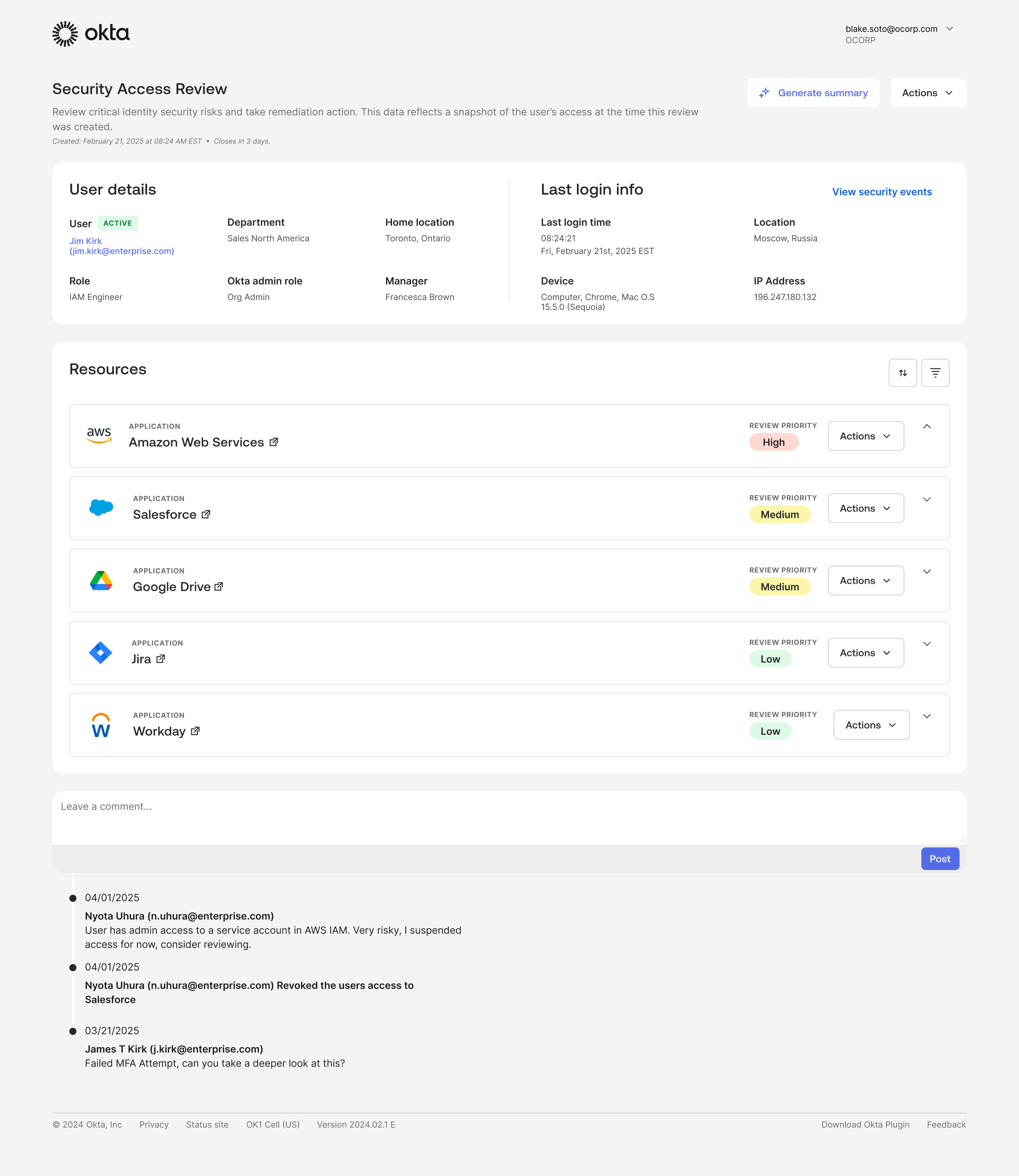
Active review
Reviewing user access and permissions for a specific employee
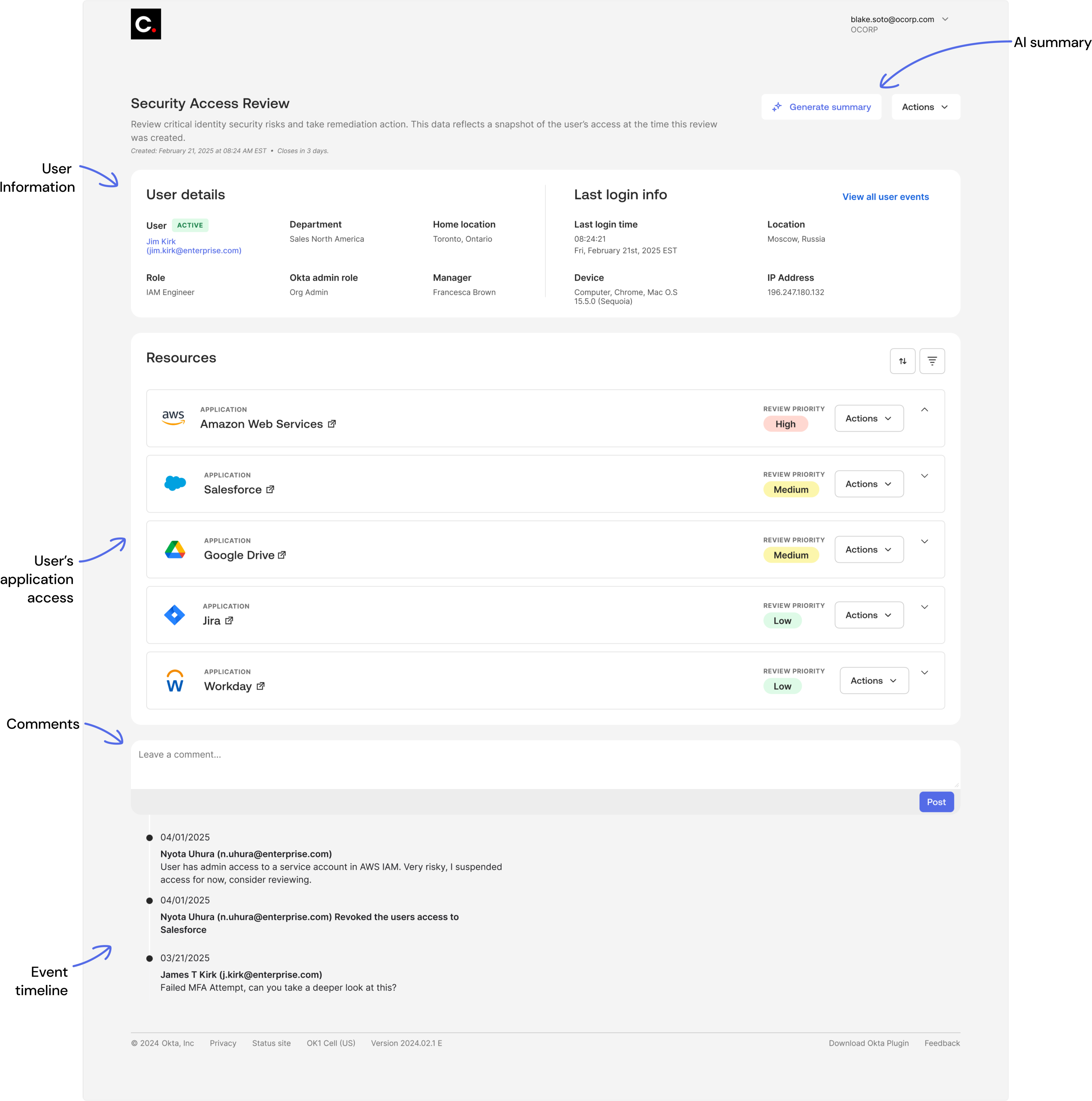
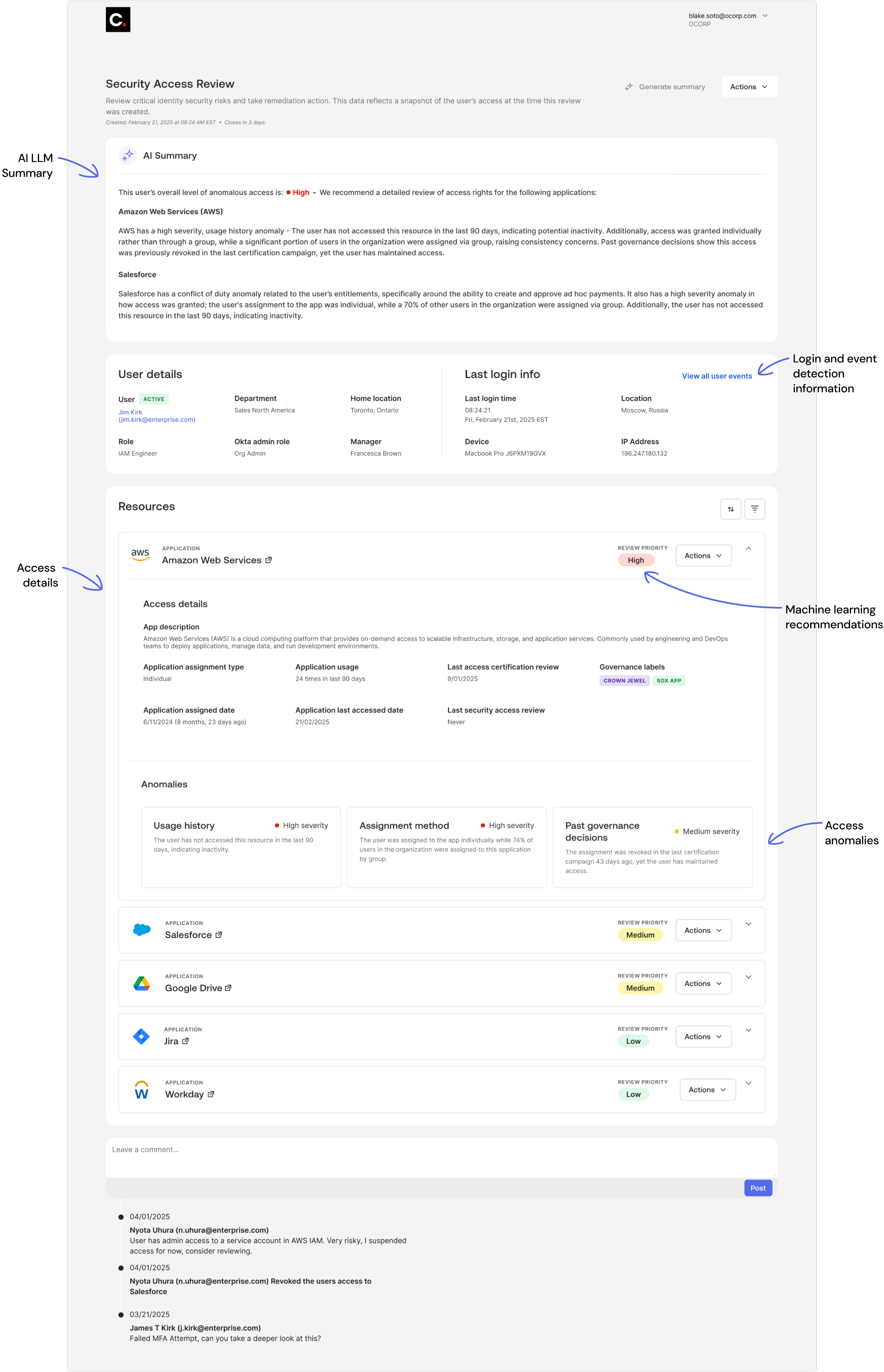
Active review
AI LLM summary & application details
Remediation actions
Revoking a user’s access to an application
View UX Case Study
OKTA
Security Access Reviews
Helping security teams detect and remediate risky access faster with AI-driven insights.
Design challenge
Access Certifications satisfy audit and compliance needs well, but follow a reactive, scheduled cadence - typically quarterly - rather than responding dynamically to identity-based security incidents. Security teams have threat detection tools, but lack a direct way to act on identity threats in real time, leaving access reviews disconnected from real-time risk detection.
How might we bridge the gap between threat detection and access certifications to enable timely, risk-aware access decisions and support a more proactive security posture?
View case study
Skills applied
User research
User interface design
Usability testing
Artificial Intelligence
Prototyping
Product strategy
Home page
List of all active and closed access reviews
Active review
Reviewing user access and permissions for a specific employee
Active review
AI LLM summary & application details
Remediation actions
Revoking a user’s access to an application
View UX Case Study
OKTA
Security Access Reviews
Helping security teams detect and remediate risky access faster with AI-driven insights.
Design challenge
Access Certifications support audit and compliance, but operate on a reactive, scheduled cadence rather than responding to identity-based security incidents in real time. Security teams can detect threats, but lack a direct way to turn those signals into timely access decisions.
How might we bridge the gap between threat detection and access reviews to enable tto enable faster, risk-aware remediation actions?
View case study
Skills applied
User research
User interface design
Usability testing
Artificial Intelligence
Prototyping
Product strategy
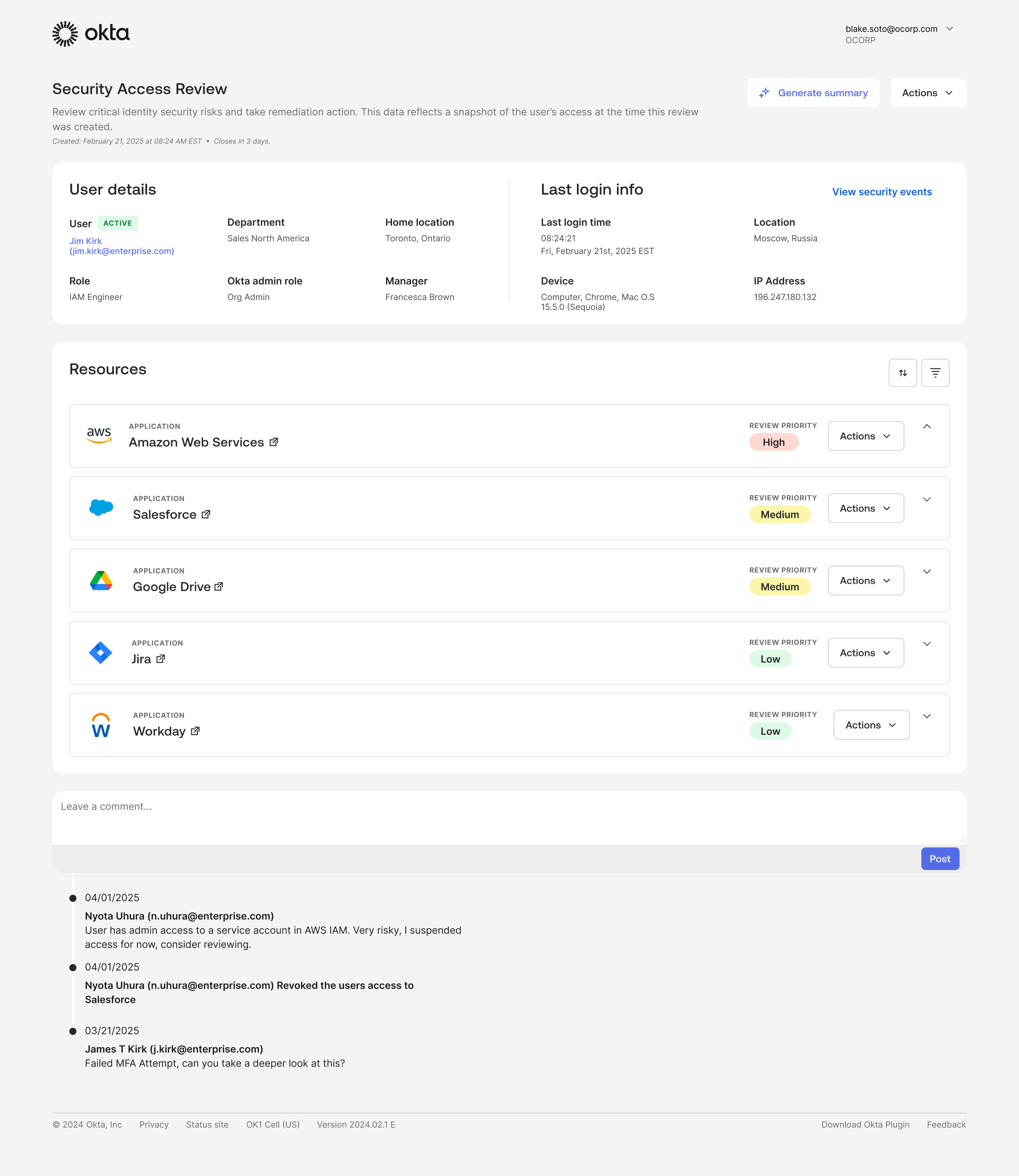
Home page
List of all active and closed access reviews
Active review
Reviewing user access and permissions for a specific employee
Active review
AI LLM summary & application details
Remediation actions
Revoking a user’s access to an application
View UX Case Study